Stay Ahead of Unauthorized File Activity and Security Risks
Atatus File Integrity Monitoring tracks every creation, modification, and deletion across your infrastructure and flags suspicious changes before they become incidents.
<1s
File change detection latency
100%
Of file events logged with full context
0
Critical changes missed with real-time alerts
4+
Compliance frameworks covered out of the box
Most teams find out about a file change after the damage is done
Capture and analyze every action across your systems in real time. Understand who did what, when, and where across your infrastructure and applications.
Someone modified /etc/.env at 3am. Nobody noticed.
It wasn't a deployment. The change came from a root session that shouldn't have been open. By the time anyone looked, the credentials had been rotated twice and the trail was cold.
The auditor asked for 90 days of file change history. We had none.
PCI-DSS 11.5 and SOC 2 both require it. Most teams know that until the audit starts and someone realizes the logs were never actually being kept anywhere searchable.
We got 4,000 file events. Zero of them told us what actually changed.
Raw inotify events tell you a file was touched. They don't tell you what the permissions were before, which process triggered it, or whether it's worth waking someone up at midnight.
Full-Context File Integrity Monitoring
Go beyond change detection. Correlate file modifications with application behavior and user activity to quickly identify risks and take action.
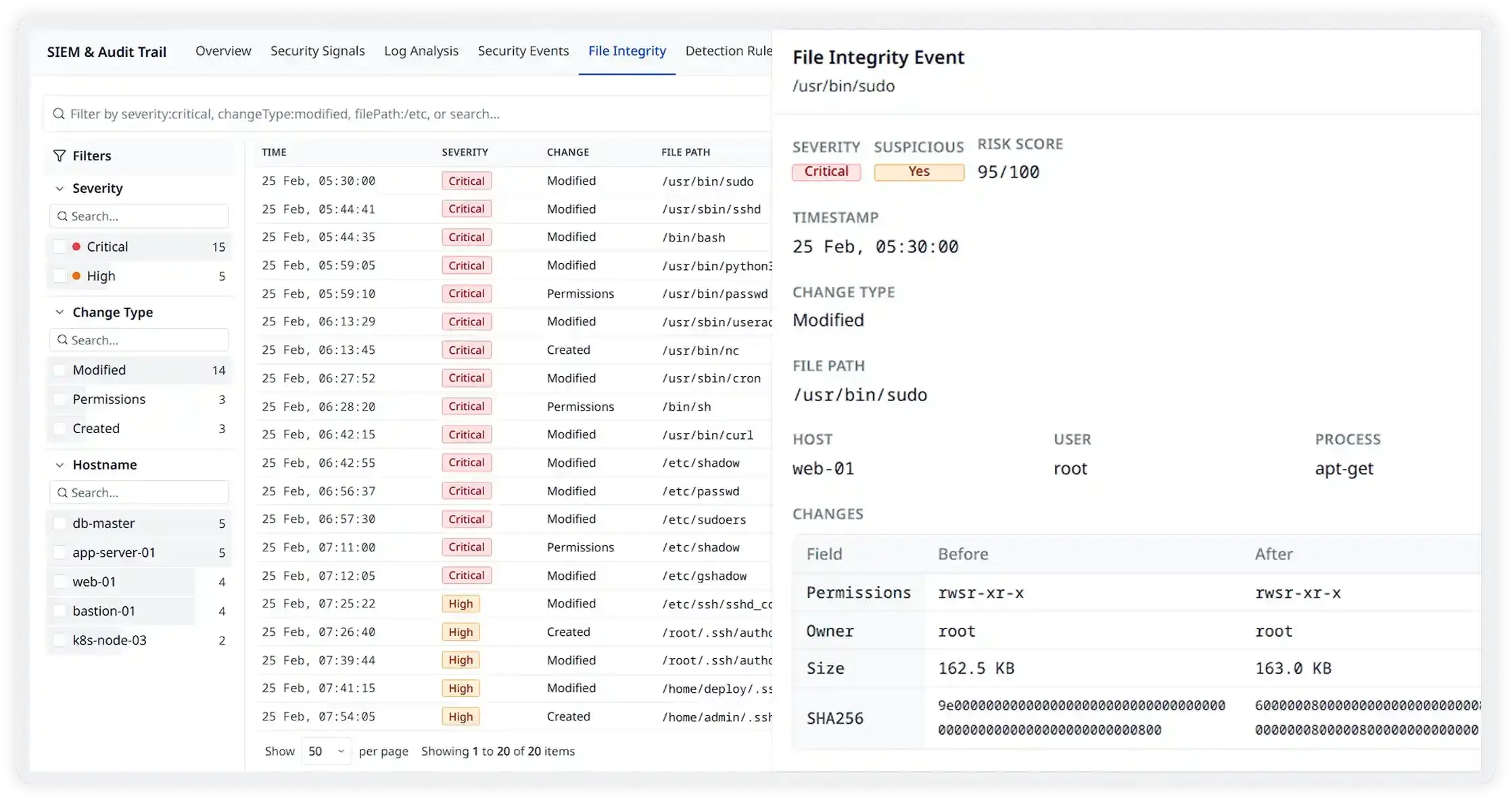
Detect Unauthorized File Changes the Moment They Happen
A single modified binary or tampered config file can be the first sign of a breach. Atatus monitors every critical file across your infrastructure and alerts you instantly with full before/after context, risk scores, and the exact user and process responsible.
- Monitor file changes across servers, containers, and cloud hosts
- Detect modifications, permission changes, and new file creation
- See the exact user, process, host, and SHA256 hash per event
- Filter by severity, change type, or hostname in real time
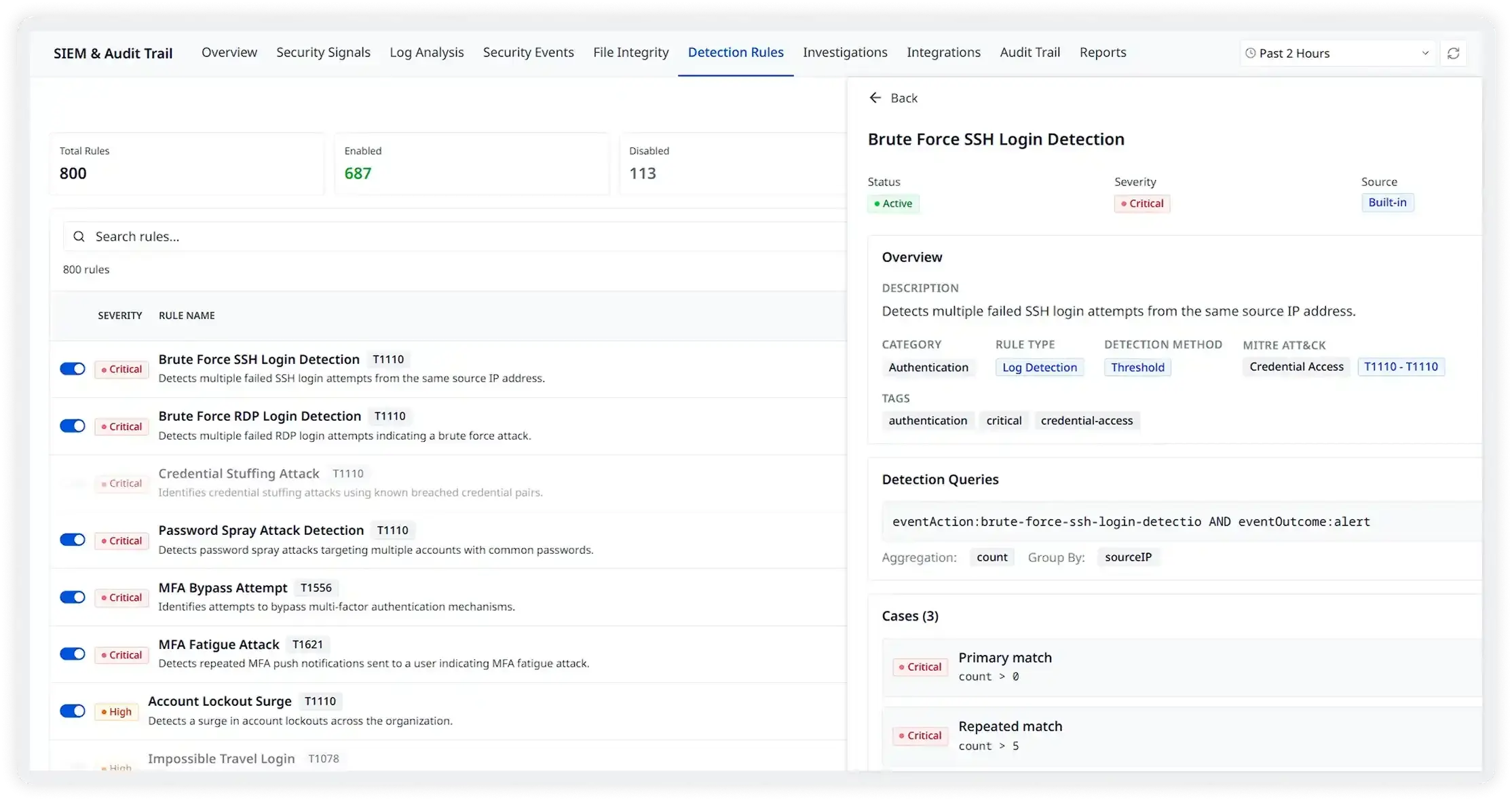
800+ Rules Ready on Day One. No Setup Required
Most teams never write a single detection rule because they don't have to. Atatus ships with 800+ built-in rules mapped to MITRE ATT&CK covering brute force, privilege escalation, credential access, and more. Enable, customize, or write your own in minutes.
- 800+ built-in rules covering critical attack techniques
- MITRE ATT&CK–mapped with severity, category, and detection method
- Write custom rules with detection queries, no proprietary language
- See live case matches and triggered alerts per rule
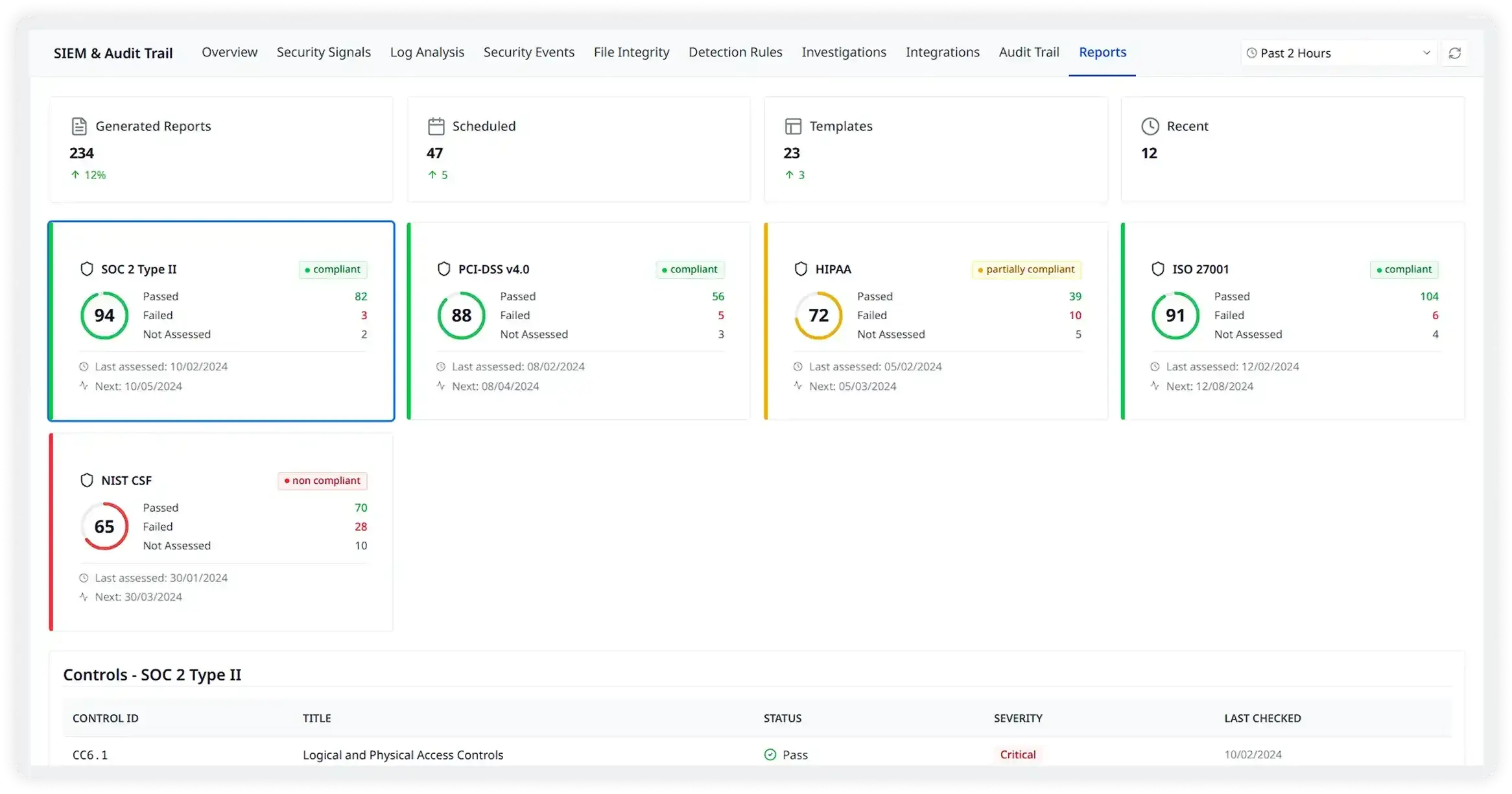
Walk Into Every Audit Fully Prepared
Auditors don't wait. Atatus continuously maps your file integrity data and security controls to SOC 2, PCI-DSS, ISO 27001, and HIPAA and generates evidence packs on demand so you're never scrambling when it counts.
- Real-time compliance scoring across SOC 2, PCI-DSS, HIPAA, and ISO 27001
- Auto-generate audit-ready reports in one click
- Track control drift and get alerted before auditors do
- Schedule and distribute reports automatically to stakeholders
Everything You Need to Monitor File Integrity
Built for security engineers and compliance teams. Complete visibility into every file event with the context to act on it.
Real-Time Change Detection
Monitor every file event including creation, modification, deletion, permission change as it happens, with sub-second detection latency.
- Track changes across all servers and environments
- Detect file content, permission, and ownership changes
- Capture exact timestamps and process context
FIM Dashboard & Analytics
A purpose-built dashboard gives your team instant visibility into change volume, affected hosts, top files, and change type breakdowns.
- Visual timeline of file change activity
- Top affected files ranked by change frequency
- Change type breakdown by creation, deletion, and modification
Rich Event Detail Panel
Drill into any event to see the full context: before/after diffs, user, process, file mode, event action, and risk score in one view
- Field-level before/after change diff
- Process, user, and host attribution per event
- Risk score with suspicious flag for instant triage
Powerful Filtering & Search
Find the exact events you need with smart filters by severity, change type, hostname, user, and file path instantly.
- Filter by severity, hostname, user, and change type
- Full-text search across file paths and event metadata
- Adjustable time windows from minutes to months
Built for Every Team That Cares About File Security
Continuous profiling replaces guesswork with evidence for every kind of slowness your team encounters.
Detect Insider Threats & Unauthorized Access
Go beyond basic file tracking. Correlate file access with traces, logs, and user sessions to understand exactly who accessed what, when, and why in one unified view.
Meet PCI-DSS, HIPAA & SOC 2 File Monitoring Requirements
Automatically satisfy file integrity monitoring mandates across major compliance frameworks with a tamper-evident, audit-ready event trail.
Reconstruct What Changed During a Breach
Use the forensic event log to reconstruct exactly which files were touched, when, by whom, and what changed, critical for post-incident investigation.
Catch Accidental or Unauthorized Config Changes
Get alerted the moment a config file, .env, or deployment manifest is changed outside of approved processes before it impacts production.
Monitor Critical Files Across Cloud Hosts
Extend FIM across AWS, GCP, and Azure instances with a single agent. No separate tooling per cloud provider needed.
Demonstrate Security Posture to Auditors
Generate on-demand evidence packs showing complete file change history, risk scores, and suspicious activity flagging for any audit window.
The event detail panel is exactly what incident responders need. Full before/after diff, risk score, user attribution, and process context in one click. It cut our investigation time by more than half.